Stay on top of your Microsoft Azure DevOps backups… Ignore this warning at your own risk.
Here’s the thing: Hundreds of thousands of companies using Azure DevOps depend on Microsoft to keep their data safe and secure. Considering how huge and established the Microsoft brand is, I don’t blame them.
However, if there’s anything we’ve learned from the news, it’s that Microsoft isn’t immune to cyberattacks.
In fact, with all their security measures in place, they were still hacked, compromised, and even experienced data loss.
So here’s a question for you: Considering the amount of headache and the thousands of dollars’ worth of damages you’ll suffer if your accounts are compromised, can you really afford to slack off with your Azure DevOps backups?
The answer should be an obvious “no.”
That’s why we’ve put together this Azure DevOps guide to help you with your backups and give your company an extra yet absolutely necessary layer of protection.
Table of Contents: Azure DevOps Backups
- Modern security threats
- Ransomware
- Hijacked account
- Malicious employees
- Backing up Azure DevOps for Compliance
- Why Azure DevOps backups really matter
- Risks of accidental deletion and long recovery times
- Azure DevOps outages and Microsoft’s breach experiences
- Microsoft-recommended practice
- How to backup Azure DevOps
Modern security threats
One of the reasons backing up Azure DevOps is so critical is the advanced security threats it’s at risk to today: ransomware, hijacked accounts, and malicious employees, to name a few.
Ransomware
Ransomware is among the most prevalent and devastating cyberattacks because of the massive amount of losses it inflicts upon businesses — whether they be financial, information, and the like.
The US Department of Justice reports that over 4,000 ransomware attacks have happened daily since January 2016 — a 300% spike from the estimated 1,000 everyday onslaughts in 2015.
In 2021, these ransomware assaults are also likely to strike businesses every 11 seconds, and its recovery will hit more than $20 billion.
Profits from ransomware more than doubled even in the last quarter of 2019 despite hackers monetizing only around 2% of their attacks.
Frequent ransomware victims include small businesses, manufacturing companies, the professional services sector, academic institutions, hospitals, and healthcare organizations.
However, web developers and technology companies aren’t exempt.
In 2019, a hacker wiped hundreds of Git source code repositories of developers in exchange for a 0.1 Bitcoin payment (equivalent to around $590).
Evidence indicates that this hacker scoured the whole Internet for Git config files, pulled out login credentials (especially the weak ones), and exploited them to access and ransom Git hosting services accounts.
Hijacked account
Another security risk to Azure DevOps is getting accounts hijacked.
For instance, using deceptive phishing emails and malicious links, a hacker may gain seamless access to a private Microsoft account when the deceived user clicks the links.
In 2018, a bug hunter discovered that an improperly configured Microsoft subdomain enabled him to link it to his Azure instance and control it and any data it receives.
The Microsoft Store and Sway apps can also be tricked into releasing verified login tokens to manipulated unconfigured domains after the user signs in on Microsoft’s Live login system.
This means any Microsoft Office account — including Azure DevOps, enterprise and corporate accounts, plus files, data, and emails — can be accessed by hackers.
The same scenario can happen for Github, too. A Canonical-owned account on Github in 2019 got its credentials compromised and exploited to make repositories, issues, etc.
With these breaches to unprotected accounts, domains, and other access points, tech companies can quickly lose their financial and data assets and burn their businesses to the ground.
Malicious employees
External malicious players are not the only security threat to Azure DevOps accounts, but even internal ones, such as employees with ill intent.
For example, in 2021, a former IT consultant deleted over 1,200 Microsoft Office accounts of the company he once worked in to avenge his being fired. This act earned him a two-year imprisonment.
It resulted in a two-day complete shutdown of the company’s operations, expenses reaching $560,000, and three-month resolutions of the issues.
Azure DevOps Backups for Compliance
The backups aren’t just meant to protect you from security threats; they’re also crucial for industry standards and regulatory compliance.
For example, if you’re preparing for an audit for System and Organization Control 2 (SOC2) or ISO27K (Information Management Standards), you’ll need to back up your cloud data assets.
In particular, SOC2 is an extensive reporting structure that applies to SaaS or technology service companies storing client data in the cloud.
SOC2 outlines five guiding Trust Service Criteria (TSC) to guarantee customer data safety. SOC2 then lets companies adopt processes and practices based on these guidelines and appropriate to their goals and operations.
These TSC principles include security, availability, processing integrity, confidentiality, and privacy.
SOC compliance is further crucial for other industry regulations, such as:
- Sarbanes-Oxley Act. Publicly traded companies under it must be SOC compliant;
- Federal Rules of Civil Procedure (FRCP). Companies should be ready to present electronic documents when lawsuits occur;
- Corporations Act 2001 Section 912A. Australian Financial Service License holders must back up their electronic data and install robust risk management systems;
- Australian Prudential Regulation Authority (APRA). Regulated super companies must be SOC compliant.
SOC compliance captures clients’ trust and makes technology service providers stand out among their competitors.
So, why are Azure DevOps and cloud data backups critical for SOC2 compliance?
Code backups enable rapid rehabilitation of services to clients and the fulfillment of the Availability TSC.
Here’s a real-life scenario. Remember the Canonical-Github account breach in 2019 mentioned earlier?
Despite the cyber onslaught, Canonical recovered the attacked repositories to their original conditions after a short downtime because they kept code backups.
An unfortunate contrast happened to Code Spaces, a well-known software collaboration and code-hosting platform that offers project management services and source code repositories with Git, Subversion, etc.
Code Spaces underwent a distributed denial-of-service attack (DDoS) and got its Amazon Web Services (AWS) account compromised in 2014.
Although the company admitted this happened often, the attacker gained access to its Amazon EC2 control panel login details.
The cybercriminal messaged Code Spaces on the panel and demanded a ransom in return for halting the DDoS attack.
Discovering that the attacker did not have its private encryption keys to access the machines, Code Spaces attempted changing its credentials to regain its control panel.
“However, the intruder had prepared for this and had already created a number of backup logins to the panel, and upon seeing us make the attempted recovery of the account, he proceeded to randomly delete artifacts from the panel,” the Code Spaces statement said on its homepage.
“In summary, most of our data, backups, machine configurations and off-site backups were either partially or completely deleted,” Code Spaces added.
Because Code Spaces missed preparing a solid data backup and recovery plan, this one devastating vulnerability shut down its hosting company within only 12 hours from the attack.
Why Azure DevOps backups really matter
Frequent Azure DevOps backups are critical for even more reasons: primarily to reduce the threat of losing data and productivity because of equipment failure and other unforeseen events.
Risks of accidental deletion and long recovery times
For one, your Azure DevOps data are at risk of accidental deletion by employees or the dreaded force push to a master repository on Github.
The force push to a master repo command can ruin the other commits pushed already to a shared repository and overwrite the remote storage’s commit history with the local history.
On Azure DevOps, if users, e.g., delete a project they think no one’s using, they can recover deleted organizations for 28 days at most. After that period, the wiped files permanently disappear.
On the other hand, developers using Github for source control can restore deleted repositories within 90 days.
While the possible recovery sounds like good news, the durations account for potential month-long downtimes wrecking tech companies’ performance and operations.
However, a deeper problem arises for deleted Azure DevOps data repositories: Microsoft lacks per-item backup. It can only retrieve entire organizations at one moment instead of individual items.
This can take Microsoft five days at most to respond, so you’re at risk of also wasting five days’ worth of operational productivity and risk permanently losing project files during the period where you lose the files and then the recovery point by Microsoft.
For example, some developers received assurance from Microsoft that they can retrieve their projects if they deleted (or accidentally erased) them.
When they did and tried to get the project files back, they discovered (to their shock and dismay) that it wasn’t doable because they can only restore an organization.
What’s more, they couldn’t restore the organization to another name in attempts of regaining the project. Since this, too, wasn’t possible, they, unfortunately, lost the project data.
Azure DevOps outages and Microsoft’s breach experiences
Azure DevOps also experiences several outages. In October 2018 alone, the platform underwent those live site incidents on four separate days.
This certainly impacts tech companies’ daily activities and poses possibly critical repercussions to their business health.
Plus, as a provider, Microsoft has experienced breaches.
One incident was in 2019 when it opened up about some compromised accounts by users of its web-based mailing services @hotmail.com and @msn.com.
Using the credentials of a customer support agent’s compromised account, hackers had possibly accessed the user’s email address, subject lines, folder names, and account names of other email addresses the agent has corresponded with.
Another incident was in March 2021, when hackers manipulated newfound vulnerabilities in Microsoft Exchange email servers to inject ransomware to potentially tens of thousands of at-risk email servers.
Microsoft-recommended practice
It’s no surprise then that Microsoft itself recommends rigorous Azure DevOps backups.
Although the company aims to keep its services always operable, they can undergo “occasional disruptions and outages.”
Microsoft continues, “In the event of an outage, you may not be able to retrieve Your Content or Data that you’ve stored.”
The company also encourages its clients to do all they can to protect their Azure DevOps data, even with tools beyond what they natively offer.
“We recommend that you regularly backup Your Content and Data that you store on the Services using Third-Party Apps and Services,” Microsoft adds.
Essential considerations when running Azure DevOps backups
The right Azure DevOps backup plan, strategy, and solution can impact your entire backup and recovery process.
Consider the following factors when backing up your Azure DevOps projects and data.
Identify what you need
Ensure your Azure DevOps backup recovery plans match your goals by determining what you need.
However, identifying your specific backups and recovery needs can take time and effort.
On top of guaranteeing high service reliability and recovery, market dynamics, rules, and laws can make it tricky to determine your needs.
A practical approach is thoroughly assessing your organization’s structure and including your stakeholders’ identified needs.
Doing so helps you develop and align your backup and recovery plan with your objectives, simplifying implementation.
Pricing of your backup solution or service
The cheapest option doesn’t always mean the best so consider your Azure DevOps backup solution’s pricing.
Is the price worth it, including its storage and backup and recovery capabilities and features?
You need the right backup service that fits your needs and supports your entire backup and recovery strategy and plans.
For example, an ideal option can be an affordable cloud-based backup technology with resource-friendly architecture that is relatively easy to use.
Consider whether your potential Azure DevOps backup service charges for data storage on top of the set price for using the solution.
Determine the post backup support you require
Your backup strategy can change depending on the workload you want to preserve.
You might need to do several types of backups for your Azure DevOps servers, projects, data, etc.
Opt for a backup service that can support the backup types you need now and in the future.
Choose a backup service that allows you to back up and restore your folders and documents and, in turn, keep your app configurations and other data.
Your backup service should also offer more sophisticated features and functionalities.
Research, read forums and reviews, and contact your backup service provider before investing in the tool.
This way, you’ll better understand all the limitations and options and whether the backup solution fits your post backup support needs.
Backup integration
Azure is a live operation system, which means DevOps backups face many challenges.
After all, DevOps environments are filled with incredibly dynamic microservices run over highly dispersed systems of linked data, computation, services, and software.
That is why it’s crucial to develop a backup plan and use a backup service that can help you adapt to a multi-tenancy or multi-region design.
Your backup process should allow successful integration into your Azure DevOps CI\CD pipeline.
The CI/CD pipeline combines the two methods of consistent delivery and continuous integration. The phase backs up your app’s dependent elements, such as datasets, configuration, and current production editions.
With the CI/CD pipeline, everything happens simultaneously, unlike the traditional waterfall software development.
If your DevOps solution does not provide a simple way to integrate backup steps, you must take additional steps to plan and implement each deployment of future app releases.
How to backup Azure DevOps
As mentioned, even Microsoft urges tech service providers to back up their data, repositories, codes, and content frequently with third-party apps and services.
Backrightup is one such platform.
It is an automated, one-click tool specifically for Azure DevOps backups, particularly if you’re keeping business-critical code.
True to its name, our software backs everything up in your Azure DevOps Repos, plus your Pipelines, Work Items, Releases, wikis, and many more.
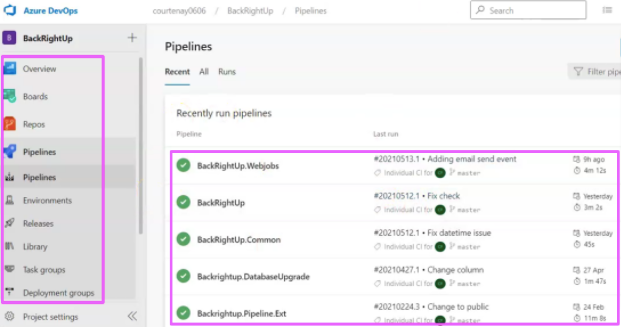
Backing up all these is tedious, which is why we do the hard work for you. And if you want to restore them, you can do so with a single click (see next image).
Another thing worth mentioning is Backrightup automatically stores each of your Azure DevOps data, repositories, codes, etc., within every single project d-a-i-l-y.
It extracts and makes copies of all these from the platform once you sign up, authorize, and connect the two tools.
On the side panel of our Backrightup dashboard, you’ll see the different backups our software made, plus updates on its latest activity.
Here’s an example of the most recent backup done for Work Items:
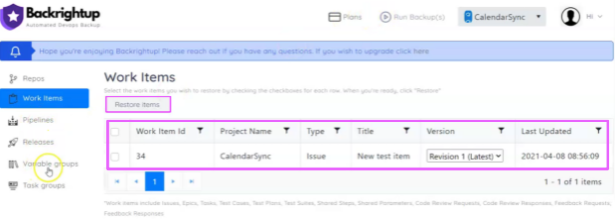
Backrightup’s report comes complete with details, such as the item’s ID number, project name, title, type, version control, and the date and time of its latest update.
The “Restore Items” button also hangs above the table if you’d like to recover any listed items by ticking the corresponding checkbox.
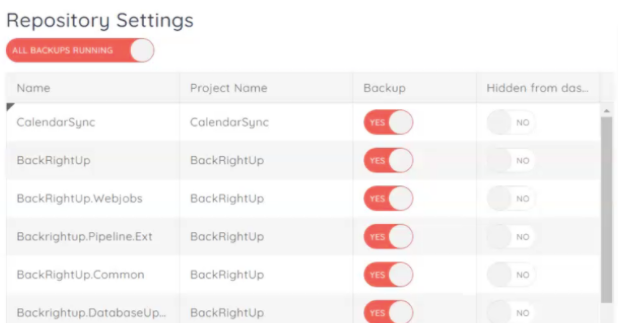
Backrightup even gives you a choice to back up only selected repositories. Head to your settings by toggling on and off the Yes and No options.
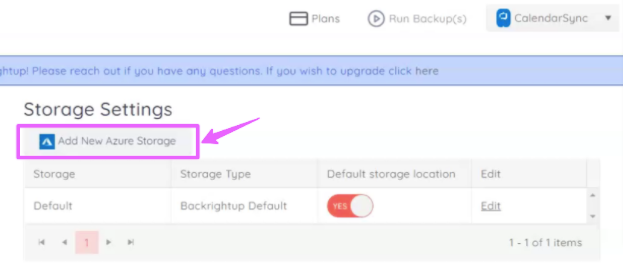
Another nifty feature is letting you add your own Azure storage location, besides our default storing collections.
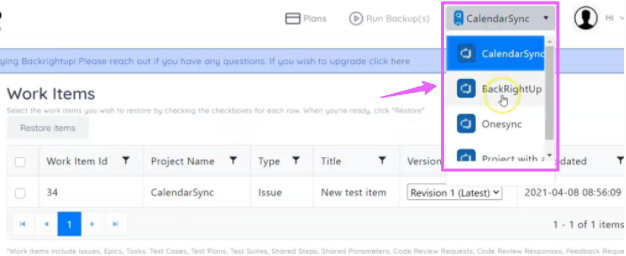
Additionally, back up different Azure DevOps projects and see them on your Backrightup dashboard at the top beside your account photo.
With these project data backups, you can restore deleted projects and individual items, unlike Microsoft’s organization-only recovery system.
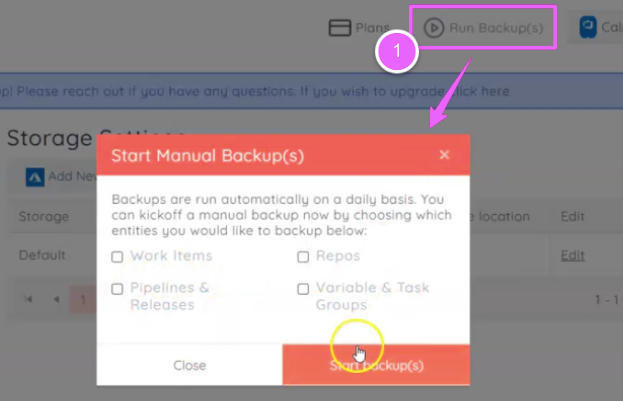
Finally, while Backrightup automates your Azure DevOps backups daily, you can opt to back up any one of the entities manually if you, say, need it right now and can’t wait for the next day.
Using our Backrightup software, you obtain highly customized and secure data backups to your preferred storage location within minutes — all without preserving your backup scripts.
Moreover, with the constantly updating Microsoft API, you won’t have to suffer from fears of your backups’ sudden disappearance and alterations.
Use Backrightup for reliable and convenient Azure DevOps Backups
Don’t put your company at risk.
Why rely on Microsoft to protect your data when they’ve succumbed to cyberattacks in the past, and they push their Azure DevOps users to work with third-party apps and services for backups?
With Backrightup, breathe a sigh of relief and have peace of mind knowing your data is backed up daily, and you can quickly restore lost data from ransomware, accidental deletion, cloud compromise, and other security risks.
If you need help with your Microsoft Azure DevOps backups, contact us now through our helpful chat widget on the homepage or email us at [email protected].